WordPress was originally launched as a blogging platform which much later became the complete web solution it is today for eCommerce stores, blogs, news sites, and enterprise-level applications. This evolution of WordPress brought many changes to its core and made it more stable and secure than its previous versions. In this post, we’ll cover the most common WordPress security vulnerabilities, along with steps you can take to secure and protect your WordPress site.
Key Takeaways:
Understanding and addressing the most common vulnerabilities in WordPress is crucial for site owners to protect their websites from potential threats.
The article highlights six common WordPress vulnerabilities: brute force attacks, SQL injections, malware, cross-site scripting, DDoS attacks, and outdated WordPress/PHP versions.
WordPress security is an ongoing process. Regularly updating WordPress core, themes, and plugins is essential to ensure that security patches are applied promptly.

Because WordPress is an open-source platform which means anybody can contribute to its core functionalities. This flexibility benefited both the developers who developed themes and plugins and the end-user who utilize them to add functionality to their WordPress sites.
This openness, however, raises some serious questions regarding the security of the platform which cannot be ignored.
This is not a flaw in the system itself but rather the structure it’s built on and considering how important that is, the WordPress security team works day and night to keep the platform secured for its end users.
Having said that as end-user we cannot simply rely on its default security mechanism as we do make a lot of changes by installing various plugins and themes to our WordPress site that can create loopholes to get exploited by hackers.
In this article, we will explore various WordPress security vulnerabilities and will learn how to avoid, and fix, them to stay secure!
Keep your website safe and secure with Sucuri's powerful tools and dedicated support team. With continuous monitoring, daily updates, and guaranteed malware removal, you can trust that your site is in good hands.
Table of Contents
WordPress Vulnerabilities & Security Issues
WordPress security is a vital concern for site owners and website owners. Understanding and addressing WordPress security issues and vulnerabilities is crucial in maintaining a secure online presence. As a site owner, it is important to be aware of potential security problems and take appropriate security measures to protect your website.
One of the common security issues revolves around the login page, which can be targeted by malicious actors attempting unauthorized access using login details obtained through various means. Implementing security features such as two-factor authentication and enforcing strong password combinations can significantly enhance website security.
Regularly updating the WordPress core, plugins, and themes is also essential to ensure that security patches are applied promptly. Additionally, site owners should consider implementing security plugins and configuring the WordPress configuration file to strengthen security measures further.
By adopting these best practices and leveraging the built-in security features of WordPress, site owners can fortify their websites against potential security vulnerabilities and ensure a robust website security framework.
We will see each issue and its solution one by one.
- Brute Force Attack
- SQL Injection
- Malware
- Cross-Site Scripting
- DDoS Attack
- Open Source CMS
- Old WordPress and PHP versions
1. Brute Force Attack
In Layman’s terms, Brute Force Attack involves a multiple try-and-error approach using hundreds of combinations to guess the right username or password. This is done using powerful algorithms and dictionaries which guess the password using some kind of context.
This kind of attack is difficult to execute but it still is one of the popular attacks executed on WordPress sites. By default, WordPress does not block a user from trying multiple failed attempts which let a human or bot try thousands of combinations per second.
How to Prevent, and Fix Brute Force Attacks
Avoiding Brute Force is fairly simple. All you have to do is create a strong password that includes Upper case letters, lower case letters, numbers, and special characters as each character has different ASCII values and it would be difficult to guess a long and complex password. Avoid using a password like johnny123 or whatsmypassword.
Also, integrate Two Factor Authentication to authenticate the users logging into your site twice. Two Factor Authentication is a great plugin to use.
You can also make an extra effort to keep your website behind a web application firewall (WAF). You can use industry leaders like Sucuri to set up the complete firewall protection of your website.
2. SQL Injection
One of the oldest hacks in the book of web hacking is injecting SQL queries to affect or completely destroy the database using any web form or input field.
Upon successful intrusion, a hacker can manipulate the MySQL database and quite possibly gain access to your WordPress admin or simply change its credentials for further damage.
This attack is usually executed by amateur to mediocre hackers who are mostly testing their hacking capabilities.
How to prevent, and fix SQL Injection
By using a plugin you can identify if your site has been a victim of SQL Injection or not. You may use WPScan or Sucuri SiteCheck to check that.
Also, update your WordPress as well as any theme or plugin which you think can be causing issues. Check their documentation and visit their support forums to report such issues so they can develop a patch.
3. Malware
Malicious code is injected into WordPress through an infected theme, outdated plugin, or script. This code can extract data from your site as well as insert malicious content that might go unnoticed due to its discreet nature.
Malware can cause mild to serious damage if not handled on time. Sometimes the whole WordPress site needs to be re-installed as it has affected the core. This can also add cost to your hosting expense as a large amount of data is transferred or is being hosted using your site.
How to prevent, and fix Malware
Usually, the malware makes its way through infected plugins and null themes. It is recommended to download themes only from trusted resources that are free from malicious content.
Security plugins like Succuri or WordFence can be used to run a full scan and fix malware. In the worst-case scenario consult with a WordPress expert.
4. Cross-Site Scripting
One of the most common attacks is Cross-Site Scripting also known as XSS attack. In this type of attack, the attacker loads a malicious JavaScript code which when loaded on the client side starts collecting data and possibly redirecting it to other malicious sites affecting the user experience.
How to prevent, and fix Cross Site Scripting XSS
To avoid this type of attack uses proper data validation across the WordPress site. Use output sanitization to ensure the right type of data is being inserted. Plugins such as Prevent XSS Vulnerability can also be used.
5. Open Source Content Management System
As a CMS, WordPress allows site owners to easily publish, organize, and modify content, making it an attractive choice for website owners across various industries. However, it’s important to be aware of potential vulnerabilities that can arise when using WordPress.
One such vulnerability involves the source code and PHP code used to build WordPress websites. Malicious actors may attempt to exploit vulnerabilities in the code to gain unauthorized access to websites or sensitive information. To mitigate these risks, it’s crucial to implement strong security measures, such as using secure login credentials and robust password combinations.
Additionally, protecting against SQL injections is essential. These attacks target user input fields, attempting to manipulate database queries and gain unauthorized access to sensitive data. Regularly updating and patching WordPress core, plugins, and themes is another crucial step in maintaining a secure WordPress environment. Security plugins can provide an extra layer of protection by actively monitoring and blocking potential threats.
Site owners should also pay attention to the configuration file, ensuring that appropriate security settings are in place. By taking these precautions and staying vigilant, site owners can protect user accounts, media files, and the overall security of their WordPress CMS.
6. DDoS Attack
Anybody who has browsed the net or manages a website may have come across the infamous DDoS attack.
Distributed Denial of Service (DDoS) is the enhanced version of Denial of Service (DoS) in which a large volume of requests are made to a web server which makes it slow and ultimately crashes.
DDoS is executed using a single source while DDoS is an organized attack executed via multiple machines across the globe. Every year millions of dollars are wasted due to this notorious web security attack.
How to Prevent, and Fix DDoS Attacks
DDoS attacks are difficult to prevent using conventional techniques. Web hosts play an important part in shielding your WordPress site from such attacks.
For example, Cloudways managed cloud hosting provider manages server security and flags anything suspicious before it can cause any damage to the customer’s website.
7. Outdated WordPress & PHP Versions
Outdated WordPress versions are more prone to get affected by a security threat. Over time hackers find their way to exploit its core and ultimately execute the attack on the sites still using outdated versions.
For the same reason, the WordPress team releases patches and newer versions with updated security mechanisms. Running older versions of PHP can cause incompatibility issues. As WordPress runs on PHP, it requires an updated version to operate properly.
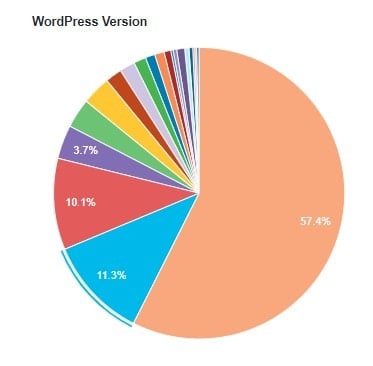
As per WordPress’s official statistics, 42.6% of users are still using various older versions of WordPress.
Whereas only 2.3% of WordPress sites are running on the latest PHP version.

How to prevent, and fix Outdated WordPress & PHP Versions
This one is an easy one. You should always update your WordPress installation to the latest version.
Make sure you always use the latest version (remember to always do a backup before upgrading). As for upgrading PHP, once you have tested your WordPress site for compatibility, you can change the version of PHP.
Pro-Tip: Using a security plugin like Sucuri can prevent the vulnerabilities mentioned above. I highly recommend it.
FAQ
Final Thoughts
We got ourselves familiar with various WordPress vulnerabilities and their possible solutions. It is worth noticing that update plays an essential role in keeping the WordPress security intact.
And when you notice any unusual activity, get on your toes and start digging until you find the problem as these security risks can cause damages in thousands of $$.
